
A Denial-of-Service (DoS) attack aims to disrupt the normal functioning of a network, service, or server by overwhelming it with a flood of internet traffic. The primary goal is to render the target unavailable to its intended users. Unlike other cyberattacks that focus on breaching data or financial theft, a DoS attack’s main objective is to cause downtime and service disruption, which can result in significant operational and financial losses.
A Denial-of-Service (DoS) attack is a malicious attempt to disrupt the normal functioning of a targeted system by overwhelming it with a flood of internet traffic. The primary goal is to exhaust the system’s resources, such as bandwidth, memory, and processing power, rendering it unavailable to legitimate users. Understanding the different types of DoS attacks can help businesses better prepare and defend against these threats.
Volume-based attacks aim to consume the bandwidth of the target site by sending an enormous amount of data. This makes it impossible for legitimate traffic to reach the site. Common examples include ICMP floods and UDP floods. In an ICMP flood, the attacker sends a large number of ICMP Echo Request (ping) packets to the target. Similarly, a UDP flood involves sending numerous UDP packets to random ports on the target machine. The target system tries to process these packets, which quickly overwhelms it.
Protocol attacks focus on exploiting weaknesses in the protocols used by the targeted system. These attacks consume server resources or intermediate communication equipment like firewalls and load balancers. Examples include SYN floods and Ping of Death. In a SYN flood, the attacker sends a series of SYN requests to initiate a TCP handshake but never completes the handshake. This leaves the server with half-open connections, consuming resources and preventing new connections. Ping of Death involves sending malformed or oversized packets to the target, causing it to crash or become unresponsive.
Application layer attacks target specific applications to exhaust server resources, such as processing power and memory. One common example is an HTTP flood, where the attacker sends numerous HTTP requests to the server, mimicking legitimate traffic. The server becomes overwhelmed trying to respond to these requests, slowing down or crashing. These attacks are particularly challenging to mitigate because they can be indistinguishable from normal traffic.
In October 2016, Dyn, a significant DNS provider, experienced one of the largest DDoS attacks in history. The attack leveraged the Mirai botnet, which comprised numerous compromised IoT devices like cameras and DVRs. These devices flooded Dyn’s servers with an overwhelming volume of traffic, causing widespread disruptions. The primary aim was to disable Dyn’s services, resulting in major websites like Twitter, Netflix, PayPal, Spotify, and Reddit going offline for hours.
The Mirai botnet exploited the weak security of many IoT devices, using default or easily guessable login credentials to take control. Once these devices were compromised, they were integrated into the botnet, which was controlled from a central server. On the day of the attack, this command server directed the botnet to target Dyn, creating a traffic surge that overwhelmed their infrastructure.
The impact of this attack was immediate and significant. Businesses relying on affected websites faced considerable disruptions. For Dyn, the attack not only posed operational challenges but also exposed vulnerabilities in their infrastructure. The use of DNS reflection techniques amplified the traffic volume, making mitigation difficult.
Despite these challenges, Dyn managed to restore services within a few hours. However, the attack persisted with additional waves throughout the day, each slightly less severe but still disruptive. This incident highlighted the critical nature of DNS services and the extensive effects of DDoS attacks on internet infrastructure.
Several key lessons emerged from this attack. Firstly, the Mirai botnet underscored the need for better security practices for IoT devices, such as changing default passwords and regularly updating firmware. Secondly, it demonstrated the importance of resilient network infrastructures. Techniques like network segmentation and load balancing can distribute traffic and prevent a single point of failure. Additionally, utilizing DDoS mitigation services can help detect and block malicious traffic, ensuring service availability during an attack. Regular network monitoring also allows for early detection of unusual activity, enabling a faster response to potential threats.
A Distributed Denial-of-Service (DDoS) attack is a more advanced form of DoS attack. In a DDoS attack, the traffic comes from multiple sources, often thousands of compromised computers, also known as a botnet. These machines, infected with malware, are controlled by the attacker to simultaneously send massive amounts of traffic to the target. The distributed nature of the attack makes it much harder to defend against, as the traffic appears to come from many different sources, complicating the process of filtering out malicious traffic.
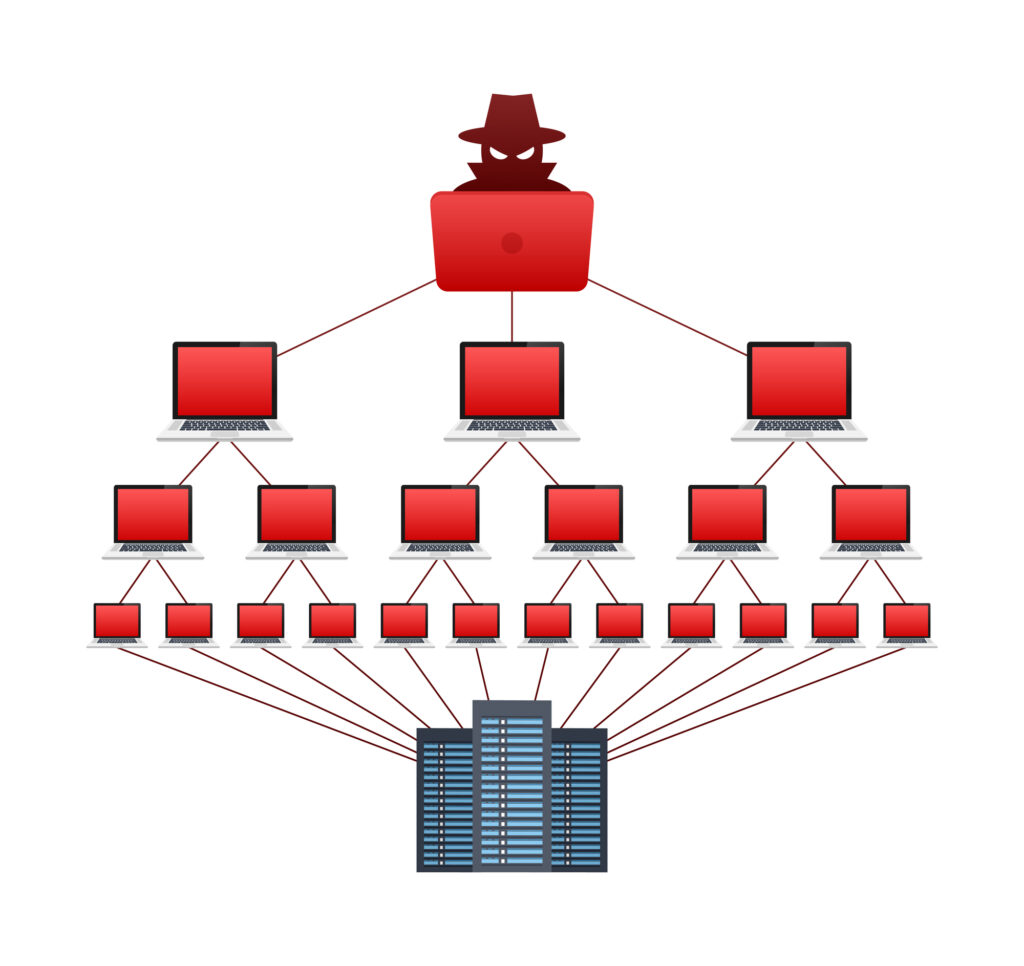
The main difference between DoS and DDoS attacks lies in the number of sources involved. A DoS attack originates from a single source, making it somewhat easier to detect and mitigate. In contrast, a DDoS attack involves multiple sources, creating a more complex and powerful threat. This distributed approach not only makes it more challenging to identify the attack’s origin but also increases the attack’s potential scale and impact.
For example, imagine trying to block a single person throwing rocks at your window (DoS) versus trying to block a coordinated effort by hundreds of people doing the same thing from different directions (DDoS). The latter is much more difficult to defend against and can cause more significant damage.
Preventing DoS attacks requires a multi-faceted approach that combines strong security practices, continuous monitoring, and strategic planning. Here’s how you can protect your business from these disruptive attacks:
One of the first lines of defense against DoS attacks is a robust firewall. Firewalls can filter out malicious traffic before it reaches your servers. To enhance protection, use a Web Application Firewall (WAF), which is designed to protect web applications by filtering and monitoring HTTP traffic. This can prevent application layer attacks that target specific services.
Additionally, consider using DDoS protection services provided by specialized security companies. These services can detect unusual traffic patterns and mitigate attacks by blocking malicious traffic. They often use a global network of data centers to absorb and disperse traffic, preventing it from overwhelming your servers.
Continuous network monitoring is essential for early detection of DoS attacks. By keeping an eye on your network traffic, you can spot anomalies that indicate an attack is underway. Set up alerts for unusual spikes in traffic or other suspicious activities. Early detection allows for a swift response, minimizing the impact of the attack.
Rate limiting controls the number of requests a user can make to your server within a specified time frame. This technique helps prevent automated tools from flooding your system with requests. For example, you can limit the number of login attempts to prevent brute force attacks or restrict the number of API calls a user can make per minute.
Distributing your network traffic across multiple servers helps prevent a single point of failure. Load balancing can manage traffic efficiently, ensuring no single server is overwhelmed. By spreading the load, you can maintain service availability even during a DoS attack. This approach also enhances overall system performance during normal operations.
The Mirai botnet attack on Dyn highlighted the vulnerabilities of IoT devices. Many IoT devices come with default usernames and passwords, making them easy targets for attackers. Ensure that all IoT devices in your network are secured with unique, strong passwords and updated with the latest firmware. Disabling unnecessary services and ports can also reduce the attack surface.
Keeping all your software up to date is crucial. Software vendors regularly release updates that patch vulnerabilities. Regular updates ensure that your systems are protected against known threats. This includes your operating systems, applications, and any security software you use.
Your employees can be your first line of defense against cyber threats. Regular training sessions can educate your staff about the signs of a DoS attack and best practices for cybersecurity. Employees should know how to recognize phishing attempts, use strong passwords, and understand the importance of regular software updates.
Having a well-defined incident response plan is essential. This plan should outline the steps to take in the event of a DoS attack, including who to contact, how to mitigate the attack, and how to restore services. Regularly review and update this plan to ensure it covers new threats and reflects changes in your infrastructure.

Partnering with IT and cyber security experts can transform the way you protect your business. At Labyrinth Technology, we recognise that managing cyber security can be overwhelming. That’s why we offer our expertise to help safeguard your business against threats like DoS attacks. Our experienced team provides more than just solutions; we deliver tailored strategies that meet your specific needs.
When you choose Labyrinth Technology, you’re not just getting tech support. We collaborate with you to evaluate your current security setup, identify potential weaknesses, and implement strong, effective defences. Our services include setting up advanced firewalls, DDoS protection, and 24/7 network monitoring to ensure your business remains secure.
We also believe in empowering your team. We offer comprehensive training to help your employees detect and respond to threats, making them an integral part of your cyber security strategy. Our proactive approach means we catch and neutralise threats before they disrupt your operations.
By partnering with us, you gain peace of mind. You can concentrate on running your business while we handle your cyber security needs. Don’t wait for a cyberattack to cause chaos. Contact Labyrinth Technology today to learn how we can help you build a robust and resilient IT infrastructure. Let’s work together to protect your business and ensure your ongoing success.
Empowering London Businesses with Efficient IT Solutions to Save Time and Stay Ahead of the Competition.