
Red teaming is a powerful cybersecurity method where ethical hackers simulate real world attacks on businesses to test and improve their security posture. It helps identify security gaps, test their response capabilities, and improve your team’s awareness of cyber threats.
For SMEs, this isn’t just an added extra, it plays an important role in protecting sensitive data and supporting long-term resilience. At Labyrinth Technology, we run hands-on red team attack simulations, including simulated phishing attacks, to help your staff spot threats early and strengthen your defences.
Red teaming is a type of security assessment where a team of ethical hackers, known as the red team, acts like a potential adversary. The goal is to gain access to systems, data, or physical spaces without being detected, just like real threat actors would.
Unlike penetration testing, which checks for known security vulnerabilities in a more structured way, red team operations focus on a more realistic, unpredictable attack simulation. This means using the same tools and attack techniques that a hacker would, to try to bypass security controls and uncover security gaps in your current security measures.
The red team’s objective isn’t to cause harm. It’s to test how your organisation responds, how fast your security teams detect an issue, and how effective your defences really are in the event of an actual attack. The end result is a much clearer picture of your organisation’s security posture.
You might think red teaming is only for big corporations, but small and medium-sized businesses are often the most at risk. You hold valuable sensitive data, from customer information to financial details. But without the budget or resources of a large enterprise, you may have security gaps you don’t know about. That’s exactly where red team exercises come in.
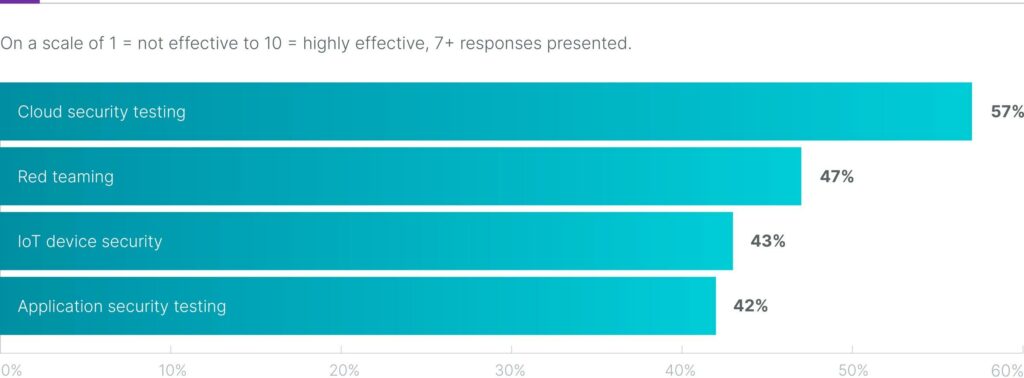
For SMEs, one of the biggest security risks is assuming you’re too small to be a target. In reality, cybercriminals often see smaller companies as easier to exploit because of weaker security systems and less formal incident response processes. A red team attack simulation helps test these areas in a controlled way. It lets you see where your defences hold up and where they fall short. Recent survey results show that 47% of organisations rate red teaming as one of the most effective offensive security testing strategies, coming second only to cloud security testing at 57%.
At Labyrinth, we specialise in offering this kind of support tailored to your business size. You don’t need to build an in-house security operations team. We bring in offensive security experts who understand how to test your systems just like a real hacker would, while keeping everything safe, ethical, and focused on improvement using threat emulation tools to ensure proper testing and results.
Understanding the difference between red team, blue team, and purple team roles helps you get a clear picture of how security teams work together to strengthen your organisation’s security posture. Each team plays a unique role in identifying and responding to cyber threats.
The red team members are made up of ethical hackers and offensive security experts who act like a potential adversary. Their goal is to simulate a targeted attack using the same tools, techniques, and attack vectors as real threat actors.
A red team’s objective is to create an attack path, bypass security controls, exploit security vulnerabilities, and see how far they can get inside your internal network without being noticed. This is not just about running a penetration test. It’s about testing how well your security teams can detect and respond to a real-world breach in action.
The blue team is your defence. These are your security professionals, IT staff, and incident response specialists who monitor, detect, and respond to security incidents. Their job is to protect the network infrastructure, close down security gaps, and manage threat detection and response capabilities in real time.
The blue team works with security software, detection tools, and vulnerability management systems to reduce the risk of a data breach. They assess and improve existing security measures, creating policies that prevent unauthorised access and reduce exposure to cyber threats.
The purple team brings both sides together. Instead of working separately, red and blue teams collaborate and share knowledge to boost the enterprise’s security posture. This team makes sure lessons from red team attack simulations are properly used to improve blue team performance.
Think of the purple team as a bridge. They make sure you’re getting the full value out of your red team exercises by helping your defence team apply the insights and plug the gaps found during the simulated attack. This results in better coordination, quicker incident response, and a stronger overall security posture.

A typical red team operation starts with planning. We gather background info and decide on our approach. That might involve physical security testing by trying to gain initial access into a building, or a simulated attack on your network infrastructure.
We might try to exploit weak security controls on your computer systems, use social engineering red teams to trick employees into giving away login details, or even run a quiet red team serves phishing campaign to see who clicks.
At Labyrinth, we run simulated phishing email attacks to test employee awareness. These aren’t harmful, but they mimic the look and feel of real attacks. If someone clicks, it doesn’t lead to a data breach, but it does show us where more training is needed.
This kind of exercise isn’t about blame. It’s about building a more alert, informed team. You’ll be able to see who fell for the phishing simulation, where your biggest security risks are, and which staff need a bit more guidance.
Over time, this approach strengthens your whole organisation’s security posture, not just in technology, but in human behaviour too.
You can’t fix what you don’t know is broken. That’s one of the core benefits of red teaming. When a red team operates and breaks into your system undetected, that’s not a failure, it’s valuable insight. It shows where your detection capabilities need improvement.
By seeing how your business reacts to a simulated attack, you learn whether your team notices anything unusual, how quickly they escalate issues, and what they do next. It’s like a fire drill, but for cyber threats.
Once we’ve finished the red team exercises, we give you a detailed report. We’ll explain exactly what we did, how we did it, and what it means for your business. Then we help you fix it. Whether that’s tightening access controls, improving vulnerability management, or rolling out new staff training, we don’t leave you guessing.
This kind of testing also gives your security personnel a chance to practise under pressure. If a real threat comes knocking, they’re not starting from scratch, they’ve already rehearsed it.
This is a common question. Pen testing, or penetration testing, is usually focused on specific systems. You might say, “Can you test our firewall, our CRM, or our web app?” A tester will look for known security vulnerabilities, try to exploit them, and produce a list of findings.
Red team operations, on the other hand, are more holistic. They don’t just look for weak points. They test the whole security posture of the organisation. This includes how people behave, how your systems react, and how your team handles an ongoing attack simulation.
A red team might use the same starting point as a pen test, but they’ll go deeper. They’ll try to pivot inside the internal network, move from system to system, and chain multiple small flaws together to reach a critical asset.
It’s more about the journey than the list. The goal is to mimic a real world attack and help you stop it before it reaches your most valuable data or systems.

At Labyrinth, we know that real security comes from being prepared, not just protected. Our red team services are designed with SMEs in mind. We combine practical knowledge, real-world experience, and a hands-on approach to make sure your business is ready for whatever comes next.
Our simulated phishing email attacks are a key part of this. These realistic exercises help staff learn what to look out for. If they fall for it, we don’t punish, we teach. You get a clear report of who clicked and when, and the option to roll out extra training through our platform. Over time, this builds strong security awareness across your whole business.
We also carry out full red team attack simulations, looking at your digital and physical security, using the same tools and methods a real attacker might. This could include social engineering techniques, testing your incident response, or trying to find a way into your network infrastructure through an unsuspecting team member.
We’re here to help you build up defences, not just test them. That means we’ll work with you after the test, helping you fix weaknesses, build up your processes, and make sure your people feel confident handling threats.
We don’t just give you a report. We give you a plan.
Red teaming gives you a real look at how your business would hold up in the face of a genuine cyber attack. It’s no longer enough to rely on security software or an annual pen testing exercise. If you want to protect your sensitive data, you need to think like the attackers do.
That’s where we come in at Labyrinth. We help businesses get ahead of real world threats by offering practical, hands-on red team operations tailored to SMEs. Our simulated phishing email attacks are a great example. They let you safely test your employees’ response to social engineering techniques, track who needs more training, and improve your security awareness across the board.
We act like the hackers, so your team can practise stopping them. Through regular red team exercises, targeted attack simulations, and insight-driven feedback, we help you tighten your security controls and boost your ability to respond quickly to any breach.
If you’re ready to take your security assessments to the next level, get in touch with us at Labyrinth. We’ll show you how red teaming can give you the peace of mind that your business, your people, and your data are all better protected against today’s most advanced cyber threats.
Empowering London Businesses with Efficient IT Solutions to Save Time and Stay Ahead of the Competition.